File and Print Servers
This chapter guides you through the installation and configuration of Samba, an open source implementation of the Server Message Block (SMB) and common Internet file system (CIFS) protocol, and vsftpd, the primary FTP server shipped with Fedora. Additionally, it explains how to use the Printer tool to configure printers.
Samba
|
Documentation for configuring and using Samba has been removed due to being outdated. Use Red Hat Enterprise Linux 9 Samba documentation instead. |
FTP
File Transfer Protocol (FTP) is one of the oldest and most commonly used protocols found on the Internet today. Its purpose is to reliably transfer files between computer hosts on a network without requiring the user to log directly into the remote host or have knowledge of how to use the remote system. It allows users to access files on remote systems using a standard set of simple commands.
This section outlines the basics of the FTP protocol, as well as configuration options for the primary FTP server shipped with Fedora, vsftpd.
The File Transfer Protocol
However, because FTP is so prevalent on the Internet, it is often required to share files to the public. System administrators, therefore, should be aware of the FTP protocol’s unique characteristics.
Multiple Ports, Multiple Modes
Unlike most protocols used on the Internet, FTP requires multiple network ports to work properly. When an FTP client application initiates a connection to an FTP server, it opens port 21 on the server — known as the command port. This port is used to issue all commands to the server. Any data requested from the server is returned to the client via a data port. The port number for data connections, and the way in which data connections are initialized, vary depending upon whether the client requests the data in active or passive mode.
The following defines these modes:
- active mode
-
Active mode is the original method used by the
FTPprotocol for transferring data to the client application. When an active mode data transfer is initiated by theFTPclient, the server opens a connection from port 20 on the server to theIPaddress and a random, unprivileged port (greater than 1024) specified by the client. This arrangement means that the client machine must be allowed to accept connections over any port above 1024. With the growth of insecure networks, such as the Internet, the use of firewalls to protect client machines is now prevalent. Because these client-side firewalls often deny incoming connections from active modeFTPservers, passive mode was devised. - passive mode
-
Passive mode, like active mode, is initiated by the
FTPclient application. When requesting data from the server, theFTPclient indicates it wants to access the data in passive mode and the server provides theIPaddress and a random, unprivileged port (greater than 1024) on the server. The client then connects to that port on the server to download the requested information.While passive mode resolves issues for client-side firewall interference with data connections, it can complicate administration of the server-side firewall. You can reduce the number of open ports on a server by limiting the range of unprivileged ports on the
FTPserver. This also simplifies the process of configuring firewall rules for the server. See Network Options for more information about limiting passive ports.
FTP Servers
Fedora ships with two different FTP servers:
-
proftpd - A fast, stable, and highly configurable FTP server.
-
vsftpd — A fast, secure
FTPdaemon which is the preferredFTPserver for Fedora. The remainder of this section focuses on vsftpd.
vsftpd
The Very Secure FTP Daemon (vsftpd) is designed from the ground up to be fast, stable, and, most importantly, secure. vsftpd is the only stand-alone FTP server distributed with Fedora, due to its ability to handle large numbers of connections efficiently and securely.
The security model used by vsftpd has three primary aspects:
-
Strong separation of privileged and non-privileged processes — Separate processes handle different tasks, and each of these processes run with the minimal privileges required for the task.
-
Tasks requiring elevated privileges are handled by processes with the minimal privilege necessary — By leveraging compatibilities found in the
libcaplibrary, tasks that usually require fullrootprivileges can be executed more safely from a less privileged process. -
Most processes run in a chroot jail — Whenever possible, processes are change-rooted to the directory being shared; this directory is then considered a chroot jail. For example, if the directory /var/ftp/ is the primary shared directory, vsftpd reassigns /var/ftp/ to the new root directory, known as /. This disallows any potential malicious hacker activities for any directories not contained below the new root directory.
Use of these security practices has the following effect on how vsftpd deals with requests:
-
The parent process runs with the least privileges required — The parent process dynamically calculates the level of privileges it requires to minimize the level of risk. Child processes handle direct interaction with the
FTPclients and run with as close to no privileges as possible. -
All operations requiring elevated privileges are handled by a small parent process — Much like the Apache
HTTPServer, vsftpd launches unprivileged child processes to handle incoming connections. This allows the privileged, parent process to be as small as possible and handle relatively few tasks. -
All requests from unprivileged child processes are distrusted by the parent process — Communication with child processes are received over a socket, and the validity of any information from child processes is checked before being acted on.
-
Most interaction with
FTPclients is handled by unprivileged child processes in a chroot jail — Because these child processes are unprivileged and only have access to the directory being shared, any crashed processes only allows the attacker access to the shared files.
Files Installed with vsftpd
The vsftpd RPM installs the daemon (/usr/sbin/vsftpd), its configuration and related files, as well as FTP directories onto the system. The following lists the files and directories related to vsftpd configuration:
-
/etc/rc.d/init.d/vsftpd— The initialization script (initscript) used by the systemctl command to start, stop, or reload vsftpd. See Starting and Stopping vsftpd for more information about using this script. -
/etc/pam.d/vsftpd— The Pluggable Authentication Modules (PAM) configuration file for vsftpd. This file specifies the requirements a user must meet to login to theFTPserver. For more information on PAM, refer to the Using Pluggable Authentication Modules (PAM) chapter of the Fedora 38 Managing Single Sign-On and Smart Cards guide. -
/etc/vsftpd/vsftpd.conf— The configuration file for vsftpd. See vsftpd Configuration Options for a list of important options contained within this file. -
/etc/vsftpd/ftpusers— A list of users not allowed to log into vsftpd. By default, this list includes theroot,bin, anddaemonusers, among others. -
/etc/vsftpd/user_list— This file can be configured to either deny or allow access to the users listed, depending on whether the userlist_deny directive is set to YES (default) or NO in/etc/vsftpd/vsftpd.conf. If/etc/vsftpd/user_listis used to grant access to users, the usernames listed must not appear in/etc/vsftpd/ftpusers. -
/var/ftp/— The directory containing files served by vsftpd. It also contains the/var/ftp/pub/directory for anonymous users. Both directories are world-readable, but writable only by therootuser.
Starting and Stopping vsftpd
The vsftpd RPM installs the /etc/rc.d/init.d/vsftpd script, which can be accessed using the systemctl command.
To start the server, as root type:
systemctl start vsftpd.service
To stop the server, as root type:
systemctl stop vsftpd.service
The restart option is a shorthand way of stopping and then starting vsftpd. This is the most efficient way to make configuration changes take effect after editing the configuration file for vsftpd.
To restart the server, as root type:
systemctl restart vsftpd.service
The condrestart (conditional restart) option only starts vsftpd if it is currently running. This option is useful for scripts, because it does not start the daemon if it is not running.
To conditionally restart the server, as root type:
systemctl condrestart vsftpd.service
By default, the vsftpd service does not start automatically at boot time. To configure the vsftpd service to start at boot time, use a service manager such as systemctl. See Services and Daemons for more information on how to configure services in Fedora.
Configuring the Firewall for FTP
By default, firewalld blocks incoming FTP connections. To allow FTP connections, as root type:
firewall-cmd --add-service=ftp
The change will be applied immediately, but will be lost next time firewalld is reloaded or the system restarted. To make it permanent, type:
firewall-cmd --permanent --add-service=ftp
For more information on configuring firewalld, see the Red Hat Enterprise Linux 7 Security Guide.
Starting Multiple Copies of vsftpd
Sometimes one computer is used to serve multiple FTP domains. This is a technique called multihoming. One way to multihome using vsftpd is by running multiple copies of the daemon, each with its own configuration file.
To do this, first assign all relevant IP addresses to network devices or alias network devices on the system. For more information about configuring network devices, device aliases, and additional information about network configuration scripts, refer to the Fedora Networking Guide.
Next, the DNS server for the FTP domains must be configured to reference the correct machine. For information about BIND and its configuration files, refer to the Fedora Networking Guide.
If there is more configuration files present in the /etc/vsftpd directory, calling systemctl start vsftpd.service results in the /etc/rc.d/init.d/vsftpd initscript starting the same number of processes as the number of configuration files. Each configuration file must have a unique name in the /etc/vsftpd/ directory and must be readable and writable only by root.
vsftpd Configuration Options
Although vsftpd may not offer the level of customization other widely available FTP servers have, it offers enough options to fill most administrator’s needs. The fact that it is not overly feature-laden limits configuration and programmatic errors.
All configuration of vsftpd is handled by its configuration file, /etc/vsftpd/vsftpd.conf. Each directive is on its own line within the file and follows the following format:
directive=value
For each directive, replace directive with a valid directive and value with a valid value.
|
Do not use spaces
There must not be any spaces between the directive, equal symbol, and the value in a directive. |
Comment lines must be preceded by a hash sign (#) and are ignored by the daemon.
For a complete list of all directives available, refer to the man page for vsftpd.conf.
|
Securing the vsftpd service
For an overview of ways to secure vsftpd, see the Red Hat Enterprise Linux 7 Security Guide. |
The following is a list of some of the more important directives within /etc/vsftpd/vsftpd.conf. All directives not explicitly found or commented out within vsftpd's configuration file are set to their default value.
Daemon Options
The following is a list of directives which control the overall behavior of the vsftpd daemon.
-
listen — When enabled, vsftpd runs in stand-alone mode. Fedora sets this value to YES. This directive cannot be used in conjunction with the listen_ipv6 directive.
The default value is NO.
-
listen_ipv6 — When enabled, vsftpd runs in stand-alone mode, but listens only to
IPv6sockets. This directive cannot be used in conjunction with the listen directive.The default value is NO.
-
session_support — When enabled, vsftpd attempts to maintain login sessions for each user through Pluggable Authentication Modules (PAM). For more information, refer to the Using Pluggable Authentication Modules (PAM) chapter of the Red Hat Enterprise Linux 6 Managing Single Sign-On and Smart Cards and the PAM man pages. . If session logging is not necessary, disabling this option allows vsftpd to run with less processes and lower privileges.
The default value is YES.
Log In Options and Access Controls
The following is a list of directives which control the login behavior and access control mechanisms.
-
anonymous_enable — When enabled, anonymous users are allowed to log in. The usernames
anonymousandftpare accepted.The default value is YES.
See Anonymous User Options for a list of directives affecting anonymous users.
-
banned_email_file — If the deny_email_enable directive is set to YES, this directive specifies the file containing a list of anonymous email passwords which are not permitted access to the server.
The default value is
/etc/vsftpd/banned_emails. -
banner_file — Specifies the file containing text displayed when a connection is established to the server. This option overrides any text specified in the ftpd_banner directive.
There is no default value for this directive.
-
cmds_allowed — Specifies a comma-delimited list of
FTPcommands allowed by the server. All other commands are rejected.There is no default value for this directive.
-
deny_email_enable — When enabled, any anonymous user utilizing email passwords specified in the
/etc/vsftpd/banned_emailsare denied access to the server. The name of the file referenced by this directive can be specified using the banned_email_file directive.The default value is NO.
-
ftpd_banner — When enabled, the string specified within this directive is displayed when a connection is established to the server. This option can be overridden by the banner_file directive.
By default vsftpd displays its standard banner.
-
local_enable — When enabled, local users are allowed to log into the system.
The default value is YES.
See Local User Options for a list of directives affecting local users.
-
pam_service_name — Specifies the PAM service name for vsftpd.
The default value is ftp. Note, in Fedora, the value is set to vsftpd.
-
The default value is NO. Note, in Fedora, the value is set to YES.
-
userlist_deny — When used in conjunction with the userlist_enable directive and set to NO, all local users are denied access unless the username is listed in the file specified by the userlist_file directive. Because access is denied before the client is asked for a password, setting this directive to NO prevents local users from submitting unencrypted passwords over the network.
The default value is YES.
-
userlist_enable — When enabled, the users listed in the file specified by the userlist_file directive are denied access. Because access is denied before the client is asked for a password, users are prevented from submitting unencrypted passwords over the network.
The default value is NO, however under Fedora the value is set to YES.
-
userlist_file — Specifies the file referenced by vsftpd when the userlist_enable directive is enabled.
The default value is /etc/vsftpd/user_list and is created during installation.
Anonymous User Options
The following lists directives which control anonymous user access to the server. To use these options, the anonymous_enable directive must be set to YES.
-
anon_mkdir_write_enable — When enabled in conjunction with the write_enable directive, anonymous users are allowed to create new directories within a parent directory which has write permissions.
The default value is NO.
-
anon_root — Specifies the directory vsftpd changes to after an anonymous user logs in.
There is no default value for this directive.
-
anon_upload_enable — When enabled in conjunction with the write_enable directive, anonymous users are allowed to upload files within a parent directory which has write permissions.
The default value is NO.
-
anon_world_readable_only — When enabled, anonymous users are only allowed to download world-readable files.
The default value is YES.
-
ftp_username — Specifies the local user account (listed in
/etc/passwd) used for the anonymousFTPuser. The home directory specified in/etc/passwdfor the user is the root directory of the anonymousFTPuser.The default value is ftp.
-
no_anon_password — When enabled, the anonymous user is not asked for a password.
The default value is NO.
-
secure_email_list_enable — When enabled, only a specified list of email passwords for anonymous logins are accepted. This is a convenient way to offer limited security to public content without the need for virtual users.
Anonymous logins are prevented unless the password provided is listed in /etc/vsftpd/email_passwords. The file format is one password per line, with no trailing white spaces.
The default value is NO.
Local User Options
The following lists directives which characterize the way local users access the server. To use these options, the local_enable directive must be set to YES.
-
chmod_enable — When enabled, the
FTPcommand SITE CHMOD is allowed for local users. This command allows the users to change the permissions on files.The default value is YES.
-
chroot_list_enable — When enabled, the local users listed in the file specified in the chroot_list_file directive are placed in a chroot jail upon log in.
If enabled in conjunction with the chroot_local_user directive, the local users listed in the file specified in the chroot_list_file directive are not placed in a chroot jail upon log in.
The default value is NO.
-
chroot_list_file — Specifies the file containing a list of local users referenced when the chroot_list_enable directive is set to YES.
The default value is /etc/vsftpd/chroot_list.
-
chroot_local_user — When enabled, local users are change-rooted to their home directories after logging in.
The default value is NO.
Avoid enabling the chroot_local_user optionEnabling chroot_local_user opens up a number of security issues, especially for users with upload privileges. For this reason, it is not recommended.
-
guest_enable — When enabled, all non-anonymous users are logged in as the user guest, which is the local user specified in the guest_username directive.
The default value is NO.
-
guest_username — Specifies the username the guest user is mapped to.
The default value is ftp.
-
local_root — Specifies the directory vsftpd changes to after a local user logs in.
There is no default value for this directive.
-
local_umask — Specifies the umask value for file creation. Note that the default value is in octal form (a numerical system with a base of eight), which includes a “0” prefix. Otherwise the value is treated as a base-10 integer.
The default value is 022.
-
passwd_chroot_enable — When enabled in conjunction with the chroot_local_user directive, vsftpd change-roots local users based on the occurrence of the /./ in the home directory field within
/etc/passwd.The default value is NO.
-
user_config_dir — Specifies the path to a directory containing configuration files bearing the name of local system users that contain specific setting for that user. Any directive in the user’s configuration file overrides those found in
/etc/vsftpd/vsftpd.conf.There is no default value for this directive.
Directory Options
The following lists directives which affect directories.
-
dirlist_enable — When enabled, users are allowed to view directory lists.
The default value is YES.
-
dirmessage_enable — When enabled, a message is displayed whenever a user enters a directory with a message file. This message resides within the current directory. The name of this file is specified in the message_file directive and is
.messageby default.The default value is NO. Note, in Fedora, the value is set to YES.
-
force_dot_files — When enabled, files beginning with a dot (
.) are listed in directory listings, with the exception of the.and..files.The default value is NO.
-
hide_ids — When enabled, all directory listings show
ftpas the user and group for each file.The default value is NO.
-
message_file — Specifies the name of the message file when using the dirmessage_enable directive.
The default value is .message.
-
text_userdb_names — When enabled, text usernames and group names are used in place of UID and GID entries. Enabling this option may slow performance of the server.
The default value is NO.
-
use_localtime — When enabled, directory listings reveal the local time for the computer instead of GMT.
The default value is NO.
File Transfer Options
The following lists directives which affect directories.
-
download_enable — When enabled, file downloads are permitted.
The default value is YES.
-
chown_uploads — When enabled, all files uploaded by anonymous users are owned by the user specified in the chown_username directive.
The default value is NO.
-
chown_username — Specifies the ownership of anonymously uploaded files if the chown_uploads directive is enabled.
The default value is root.
-
write_enable — When enabled,
FTPcommands which can change the file system are allowed, such as DELE, RNFR, and STOR.The default value is YES.
Logging Options
The following lists directives which affect vsftpd's logging behavior.
-
dual_log_enable — When enabled in conjunction with xferlog_enable, vsftpd writes two files simultaneously: a wu-ftpd-compatible log to the file specified in the xferlog_file directive (
/var/log/xferlogby default) and a standard vsftpd log file specified in the vsftpd_log_file directive (/var/log/vsftpd.logby default).The default value is NO.
-
log_ftp_protocol — When enabled in conjunction with xferlog_enable and with xferlog_std_format set to NO, all
FTPcommands and responses are logged. This directive is useful for debugging.The default value is NO.
-
syslog_enable — When enabled in conjunction with xferlog_enable, all logging normally written to the standard vsftpd log file specified in the vsftpd_log_file directive (
/var/log/vsftpd.logby default) is sent to the system logger instead under theFTPDfacility.The default value is NO.
-
vsftpd_log_file — Specifies the vsftpd log file. For this file to be used, xferlog_enable must be enabled and xferlog_std_format must either be set to NO or, if xferlog_std_format is set to YES, dual_log_enable must be enabled. It is important to note that if syslog_enable is set to YES, the system log is used instead of the file specified in this directive.
The default value is
/var/log/vsftpd.log. -
xferlog_enable — When enabled, vsftpd logs connections (vsftpd format only) and file transfer information to the log file specified in the vsftpd_log_file directive (
/var/log/vsftpd.logby default). If xferlog_std_format is set to YES, file transfer information is logged but connections are not, and the log file specified in xferlog_file (/var/log/xferlogby default) is used instead. It is important to note that both log files and log formats are used if dual_log_enable is set to YES.The default value is NO. Note, in Fedora, the value is set to YES.
-
xferlog_file — Specifies the wu-ftpd-compatible log file. For this file to be used, xferlog_enable must be enabled and xferlog_std_format must be set to YES. It is also used if dual_log_enable is set to YES.
The default value is
/var/log/xferlog. -
xferlog_std_format — When enabled in conjunction with xferlog_enable, only a wu-ftpd-compatible file transfer log is written to the file specified in the xferlog_file directive (
/var/log/xferlogby default). It is important to note that this file only logs file transfers and does not log connections to the server.The default value is NO. Note, in Fedora, the value is set to YES.
|
Maintaining compatibility with older log file formats
To maintain compatibility with log files written by the older wu-ftpd To both log connections in vsftpd format and maintain a wu-ftpd-compatible file transfer log, set dual_log_enable to YES. If maintaining a wu-ftpd-compatible file transfer log is not important, either set xferlog_std_format to NO, comment the line with a hash sign (#), or delete the line entirely. |
Network Options
The following lists directives which affect how vsftpd interacts with the network.
-
accept_timeout — Specifies the amount of time for a client using passive mode to establish a connection.
The default value is 60.
-
anon_max_rate — Specifies the maximum data transfer rate for anonymous users in bytes per second.
The default value is 0, which does not limit the transfer rate.
-
connect_from_port_20 When enabled, vsftpd runs with enough privileges to open port 20 on the server during active mode data transfers. Disabling this option allows vsftpd to run with less privileges, but may be incompatible with some
FTPclients.The default value is NO. Note, in Fedora, the value is set to YES.
-
connect_timeout — Specifies the maximum amount of time a client using active mode has to respond to a data connection, in seconds.
The default value is 60.
-
data_connection_timeout — Specifies maximum amount of time data transfers are allowed to stall, in seconds. Once triggered, the connection to the remote client is closed.
The default value is 300.
-
ftp_data_port — Specifies the port used for active data connections when connect_from_port_20 is set to YES.
The default value is 20.
-
idle_session_timeout — Specifies the maximum amount of time between commands from a remote client. Once triggered, the connection to the remote client is closed.
The default value is 300.
-
listen_address — Specifies the
IPaddress on which vsftpd listens for network connections.There is no default value for this directive.
Running multiple copies of vsftpdIf running multiple copies of vsftpd serving different
IPaddresses, the configuration file for each copy of the vsftpd daemon must have a different value for this directive. See Starting Multiple Copies of vsftpd for more information about multihomedFTPservers. -
listen_address6 — Specifies the
IPv6address on which vsftpd listens for network connections when listen_ipv6 is set to YES.There is no default value for this directive.
Running multiple copies of vsftpdIf running multiple copies of vsftpd serving different
IPaddresses, the configuration file for each copy of the vsftpd daemon must have a different value for this directive. See Starting Multiple Copies of vsftpd for more information about multihomedFTPservers. -
listen_port — Specifies the port on which vsftpd listens for network connections.
The default value is 21.
-
local_max_rate — Specifies the maximum rate data is transferred for local users logged into the server in bytes per second.
The default value is 0, which does not limit the transfer rate.
-
max_clients — Specifies the maximum number of simultaneous clients allowed to connect to the server when it is running in standalone mode. Any additional client connections would result in an error message.
The default value is 0, which does not limit connections.
-
max_per_ip — Specifies the maximum of clients allowed to connected from the same source
IPaddress.The default value is 0, which does not limit connections.
-
pasv_address — Specifies the
IPaddress for the public facingIPaddress of the server for servers behind Network Address Translation (NAT) firewalls. This enables vsftpd to hand out the correct return address for passive mode connections.There is no default value for this directive.
-
pasv_enable — When enabled, passive mode connects are allowed.
The default value is YES.
-
pasv_max_port — Specifies the highest possible port sent to the
FTPclients for passive mode connections. This setting is used to limit the port range so that firewall rules are easier to create.The default value is 0, which does not limit the highest passive port range. The value must not exceed 65535.
-
pasv_min_port — Specifies the lowest possible port sent to the
FTPclients for passive mode connections. This setting is used to limit the port range so that firewall rules are easier to create.The default value is 0, which does not limit the lowest passive port range. The value must not be lower 1024.
-
pasv_promiscuous — When enabled, data connections are not checked to make sure they are originating from the same
IPaddress. This setting is only useful for certain types of tunneling.Avoid enabling the pasv_promiscuous optionDo not enable this option unless absolutely necessary as it disables an important security feature which verifies that passive mode connections originate from the same
IPaddress as the control connection that initiates the data transfer.The default value is NO.
-
port_enable — When enabled, active mode connects are allowed.
The default value is YES.
Recursos adicionais
For more information about vsftpd, refer to the following resources.
Installed Documentation
-
The
/usr/share/doc/vsftpd/directory — This directory contains aREADMEwith basic information about the software. TheTUNINGfile contains basic performance tuning tips and theSECURITY/directory contains information about the security model employed by vsftpd. -
vsftpd related man pages — There are a number of man pages for the daemon and configuration files. The following lists some of the more important man pages.
- Server Applications
-
-
man vsftpd — Describes available command line options for vsftpd.
-
- Configuration Files
-
-
man vsftpd.conf — Contains a detailed list of options available within the configuration file for vsftpd.
-
man 5 hosts_access — Describes the format and options available within the TCP wrappers configuration files:
hosts.allowandhosts.deny.
-
Useful Websites
-
https://security.appspot.com/vsftpd.html — The vsftpd project page is a great place to locate the latest documentation and to contact the author of the software.
-
https://slacksite.com/other/ftp.html — This website provides a concise explanation of the differences between active and passive mode
FTP. -
https://www.ietf.org/rfc/rfc0959.txt — The original Request for Comments (RFC) of the
FTPprotocol from the IETF.
Printer Configuration
The Printers configuration tool serves for printer configuring, maintenance of printer configuration files, print spool directories and print filters, and printer classes management.
The tool is based on the Common Unix Printing System (CUPS). If you upgraded the system from a previous Fedora version that used CUPS, the upgrade process preserved the configured printers.
|
Using the CUPS web application or command-line tools
You can perform the same and additional operations on printers directly from the CUPS web application or command line. To access the application, in a web browser, go to http://localhost:631/. For CUPS manuals refer to the links on the |
Starting the Printers Configuration Tool
With the Printers configuration tool you can perform various operations on existing printers and set up new printers. You can also use CUPS directly (go to http://localhost:631/ to access the CUPS web application).
To start the Printers configuration tool if using the GNOME desktop, press the Super key to enter the Activities Overview, type Printers, and then press Enter. The Printers configuration tool appears. The Super key appears in a variety of guises, depending on the keyboard and other hardware, but often as either the Windows or Command key, and typically to the left of the Spacebar.
The Printers window depicted in Printers Configuration window appears.
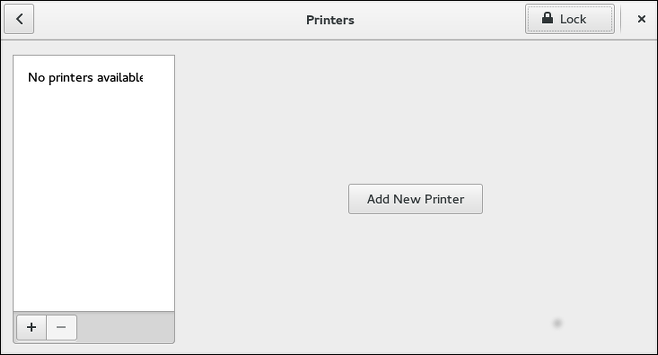
Starting Printer Setup
Printer setup process varies depending on the printer queue type.
If you are setting up a local printer connected with USB, the printer is discovered and added automatically. You will be prompted to confirm the packages to be installed and provide an administrator or the root user password. Local printers connected with other port types and network printers need to be set up manually.
Follow this procedure to start a manual printer setup:
-
Start the Printers configuration tool (refer to Starting the Printers Configuration Tool).
-
Select
Unlockto enable changes to be made. In theAuthentication Requiredbox, type an administrator or therootuser password and confirm. -
Select the plus sign to open the
Add a New Printerdialog. Select the printer from the list or enter its address below.
Adding a Local Printer
Follow this procedure to add a local printer connected with other than a serial port:
-
Open the
Add a New Printerdialog (refer to Starting Printer Setup). -
If the device does not appear automatically, select the port to which the printer is connected in the list on the left (such as
Serial Port #1orLPT #1). -
On the right, enter the connection properties:
- for
Enter URI -
URI(for example file:/dev/lp0) - for
Serial Port -
Baud Rate
- for
Parity
Data Bits
Flow Control
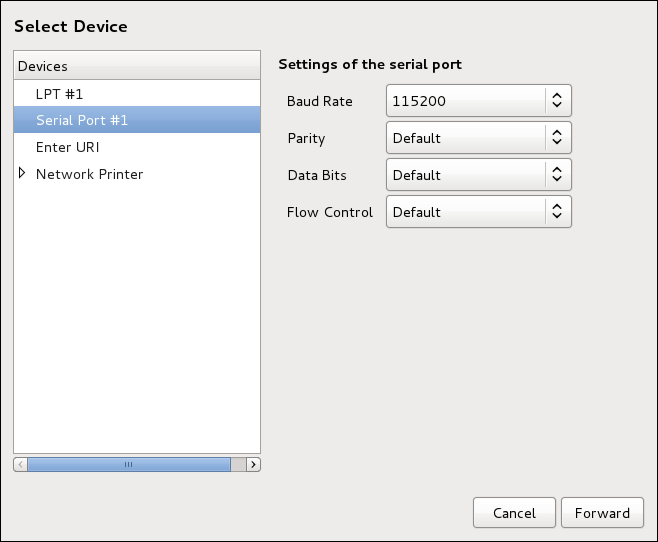
-
Click Forward.
-
Select the printer model. See Selecting the Printer Model and Finishing for details.
Adding an AppSocket/HP JetDirect printer
Follow this procedure to add an AppSocket/HP JetDirect printer:
-
Open the
Add a New Printerdialog (refer to Starting the Printers Configuration Tool). -
In the list on the left, select .
-
On the right, enter the connection settings:
Hostname-
Printer host name or
IPaddress. Port Number-
Printer port listening for print jobs (
9100by default).
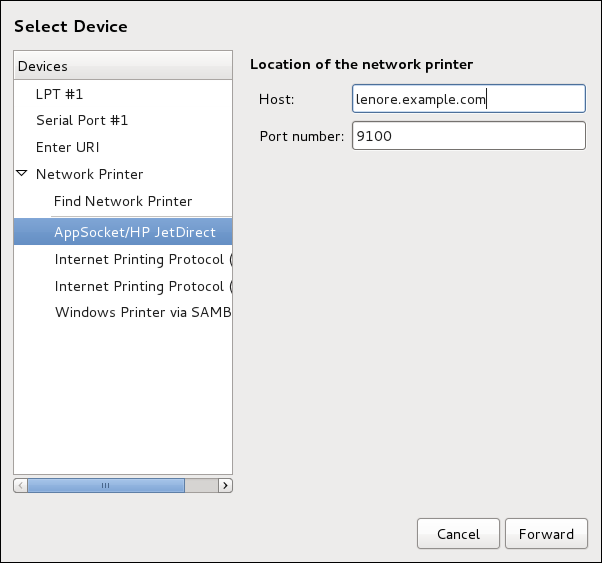
-
Click Forward.
-
Select the printer model. See Selecting the Printer Model and Finishing for details.
Adding an IPP Printer
An IPP printer is a printer attached to a different system on the same TCP/IP network. The system this printer is attached to may either be running CUPS or simply configured to use IPP.
If a firewall is enabled on the printer server, then the firewall must be configured to allow incoming TCP connections on port 631. Note that the CUPS browsing protocol allows client machines to discover shared CUPS queues automatically. To enable this, the firewall on the client machine must be configured to allow incoming UDP packets on port 631.
Follow this procedure to add an IPP printer:
-
Open the
Printersdialog (refer to Starting Printer Setup). -
In the list of devices on the left, select Network Printer and
Internet Printing Protocol (ipp)orInternet Printing Protocol (https). -
On the right, enter the connection settings:
Host-
The host name of the
IPPprinter. Queue-
The queue name to be given to the new queue (if the box is left empty, a name based on the device node will be used).
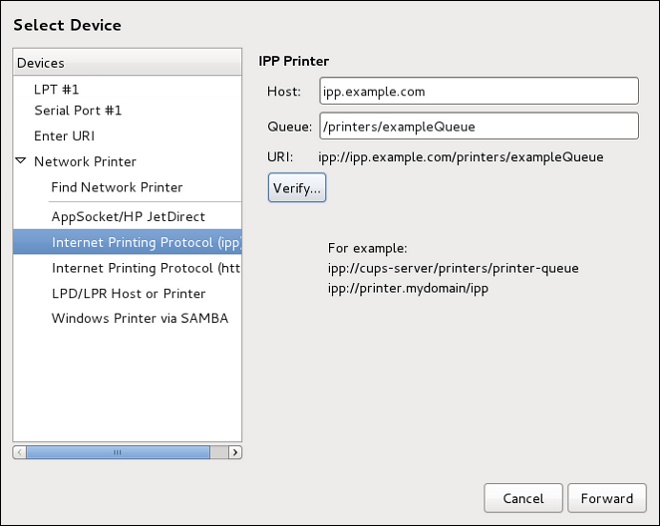
-
Optionally, click Verify to detect the printer.
-
Click Forward to continue.
-
Select the printer model. See Selecting the Printer Model and Finishing for details.
Adding an LPD/LPR Host or Printer
Follow this procedure to add an LPD/LPR host or printer:
-
Open the
New Printerdialog (refer to Starting Printer Setup). -
In the list of devices on the left, select .
-
On the right, enter the connection settings:
Host-
The host name of the LPD/LPR printer or host.
Optionally, click Probe to find queues on the LPD host.
Queue-
The queue name to be given to the new queue (if the box is left empty, a name based on the device node will be used).
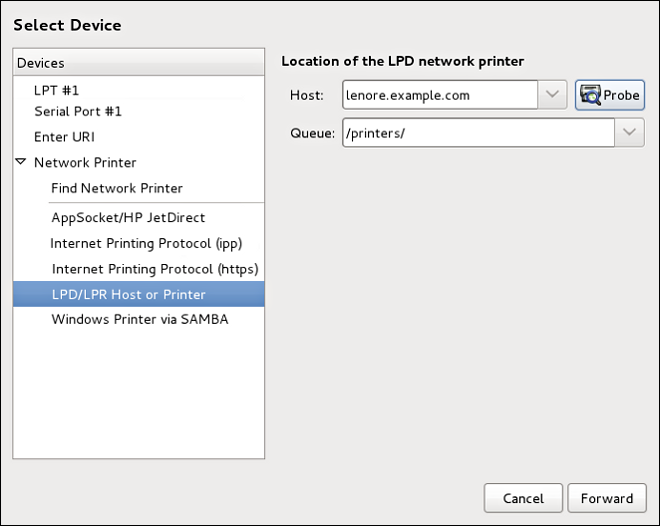
-
Click Forward to continue.
-
Select the printer model. See Selecting the Printer Model and Finishing for details.
Adding a Samba (SMB) printer
Follow this procedure to add a Samba printer:
|
Installing the samba-client package
Note that in order to add a Samba printer, you need to have the samba-client package installed. You can do so by running, as dnf install samba-client
For more information on installing packages with DNF, refer to Installing Packages. |
-
Open the
New Printerdialog (refer to Starting Printer Setup). -
In the list on the left, select .
-
Enter the SMB address in the
smb://field. Use the format computer name/printer share. In Adding a SMB printer, the computer name is dellbox and the printer share is r2.
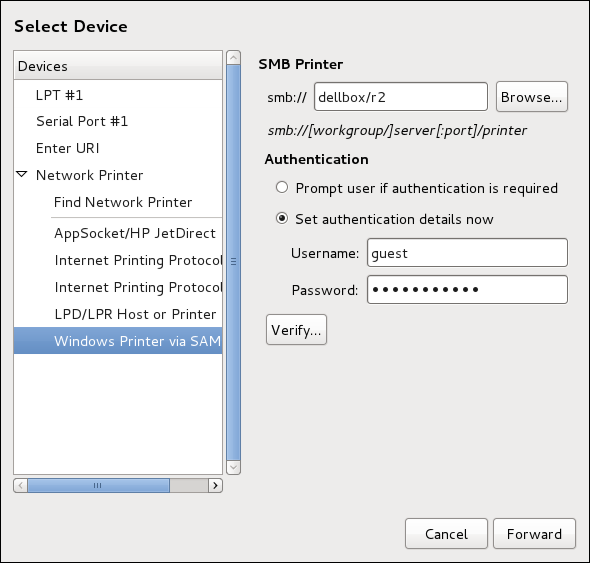
-
Click Browse to see the available workgroups/domains. To display only queues of a particular host, type in the host name (NetBios name) and click Browse.
-
Select either of the options:
-
Prompt user if authentication is required: user name and password are collected from the user when printing a document. -
Set authentication details now: provide authentication information now so it is not required later. In theUsernamefield, enter the user name to access the printer. This user must exist on the SMB system, and the user must have permission to access the printer. The default user name is typicallyguestfor Windows servers, ornobodyfor Samba servers.
-
-
Enter the
Password(if required) for the user specified in theUsernamefield.
|
Be careful when choosing a password
Samba printer user names and passwords are stored in the printer server as unencrypted files readable by Therefore, when you choose a user name and password to access a Samba printer, it is advisable that you choose a password that is different from what you use to access your local Fedora system. If there are files shared on the Samba print server, it is recommended that they also use a password different from what is used by the print queue. |
-
Click Verify to test the connection. Upon successful verification, a dialog box appears confirming printer share accessibility.
-
Click Forward.
-
Select the printer model. See Selecting the Printer Model and Finishing for details.
Selecting the Printer Model and Finishing
Once you have properly selected a printer connection type, the system attempts to acquire a driver. If the process fails, you can locate or search for the driver resources manually.
Follow this procedure to provide the printer driver and finish the installation:
-
In the window displayed after the automatic driver detection has failed, select one of the following options:
-
Select printer from database— the system chooses a driver based on the selected make of your printer from the list ofMakes. If your printer model is not listed, chooseGeneric. -
Provide PPD file— the system uses the provided PostScript Printer Description (PPD) file for installation. A PPD file may also be delivered with your printer as being normally provided by the manufacturer. If the PPD file is available, you can choose this option and use the browser bar below the option description to select the PPD file. -
Search for a printer driver to download— enter the make and model of your printer into theMake and modelfield to search on OpenPrinting.org for the appropriate packages.
-
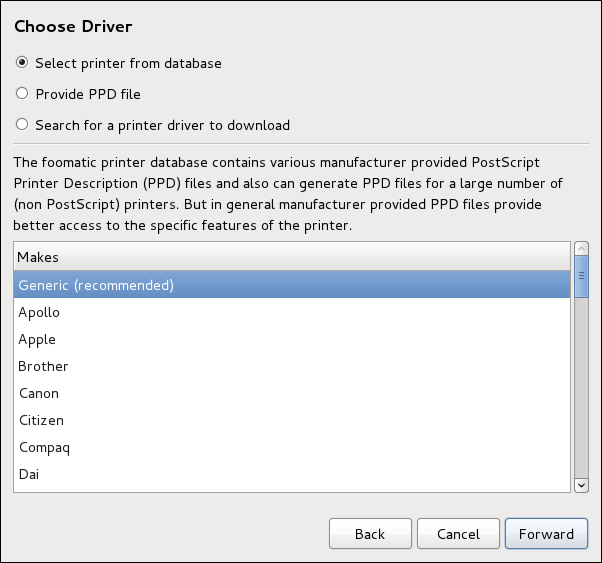
-
Depending on your previous choice provide details in the area displayed below:
-
Printer brand for the
Select printer from databaseoption. -
PPD file location for the
Provide PPD fileoption. -
Printer make and model for the
Search for a printer driver to downloadoption.
-
-
Click Forward to continue.
-
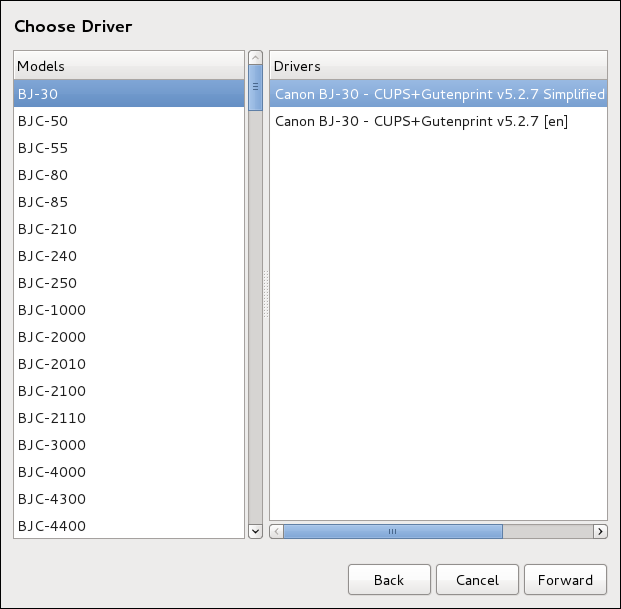
If applicable for your option, window shown in Selecting a printer model appears. Choose the corresponding model in the
Modelscolumn on the left.
|
Selecting a printer driver
On the right, the recommended printer driver is automatically selected; however, you can select another available driver. The print driver processes the data that you want to print into a format the printer can understand. Since a local printer is attached directly to your computer, you need a printer driver to process the data that is sent to the printer. |
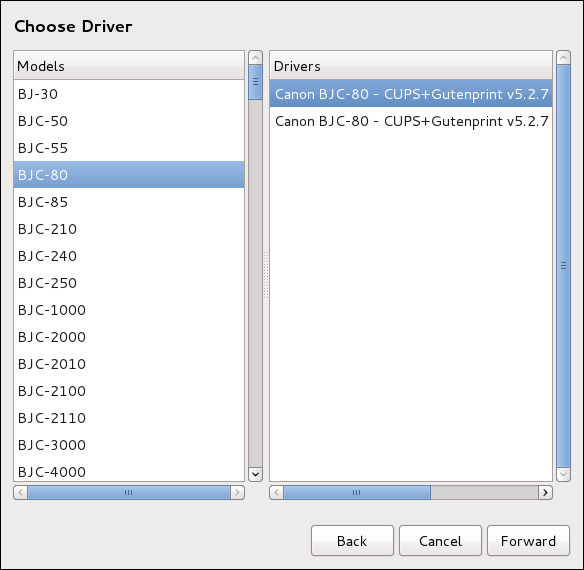
-
Click Forward.
-
Under the
Describe Printerenter a unique name for the printer in thePrinter Namefield. The printer name can contain letters, numbers, dashes (-), and underscores (_); it must not contain any spaces. You can also use theDescriptionandLocationfields to add further printer information. Both fields are optional, and may contain spaces.
-
Click Apply to confirm your printer configuration and add the print queue if the settings are correct. Click Back to modify the printer configuration.
-
After the changes are applied, a dialog box appears allowing you to print a test page. Click Print Test Page to print a test page now. Alternatively, you can print a test page later as described in Printing a Test Page.
Printing a Test Page
After you have set up a printer or changed a printer configuration, print a test page to make sure the printer is functioning properly:
-
Right-click the printer in the
Printingwindow and clickProperties. -
In the Properties window, click
Settingson the left. -
On the displayed
Settingstab, click the Print Test Page button.
Modifying Existing Printers
To delete an existing printer, in the Printer configuration window, select the printer and go to . Confirm the printer deletion. Alternatively, press the Delete key.
To set the default printer, right-click the printer in the printer list and click the Set As Default button in the context menu.
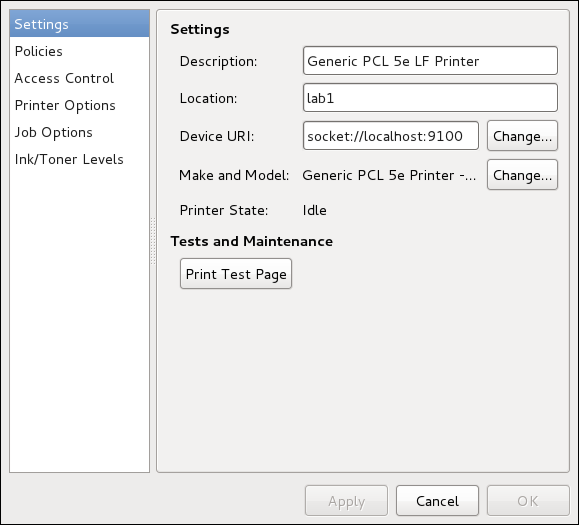
The Settings Page
To change printer driver configuration, double-click the corresponding name in the Printer list and click the Settings label on the left to display the Settings page.
You can modify printer settings such as make and model, print a test page, change the device location (URI), and more.
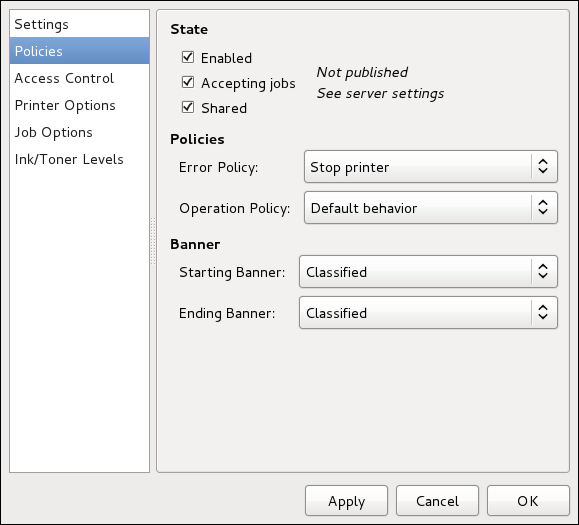
The Policies Page
Click the Policies button on the left to change settings in printer state and print output.
You can select the printer states, configure the Error Policy of the printer (you can decide to abort the print job, retry, or stop it if an error occurs).
You can also create a banner page (a page that describes aspects of the print job such as the originating printer, the user name from the which the job originated, and the security status of the document being printed): click the Starting Banner or Ending Banner drop-down menu and choose the option that best describes the nature of the print jobs (for example, confidential).
On the Policies page, you can mark a printer as shared: if a printer is shared, users published on the network can use it. To allow the sharing function for printers, go to and select Publish shared printers connected to this system.
Make sure that the firewall allows incoming TCP connections to port 631, the port for the Network Printing Server (IPP) protocol. To allow IPP traffic through the firewall on Fedora 38, make use of firewalld's IPP service. To do so, proceed as follows:
-
To start the graphical firewall-config tool, press the Super key to enter the Activities Overview, type firewall and then press Enter. The
Firewall Configurationwindow opens. You will be prompted for an administrator orrootpassword.
Alternatively, to start the graphical firewall configuration tool using the command line, enter the following command as root user:
~]# firewall-config
The Firewall Configuration window opens.
Look for the word “Connected” in the lower left corner. This indicates that the firewall-config tool is connected to the user space daemon, firewalld.
To immediately change the current firewall settings, ensure the drop-down selection menu labeled Configuration is set to Runtime. Alternatively, to edit the settings to be applied at the next system start, or firewall reload, select Permanent from the drop-down list.
-
Select the
Zonestab and then select the firewall zone to correspond with the network interface to be used. The default is thepubliczone. TheInterfacestab shows what interfaces have been assigned to a zone. -
Select the
Servicestab and then select theippservice to enable sharing. Theipp-clientservice is required for accessing network printers. -
Close the firewall-config tool.
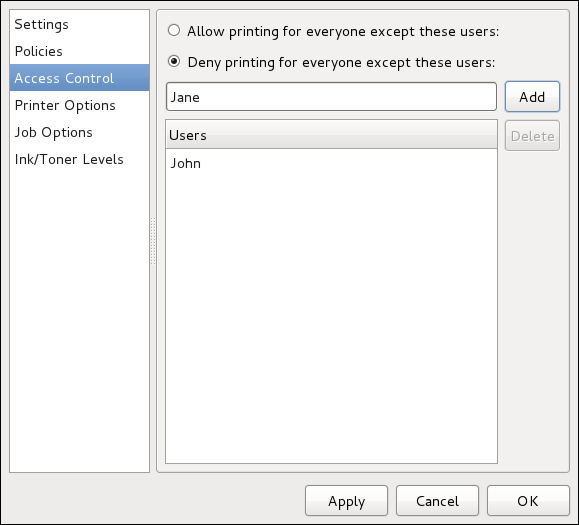
You can change user-level access to the configured printer on the Access Control page. Click the Access Control label on the left to display the page. Select either Allow printing for everyone except these users or Deny printing for everyone except these users and define the user set below: enter the user name in the text box and click the Add button to add the user to the user set.
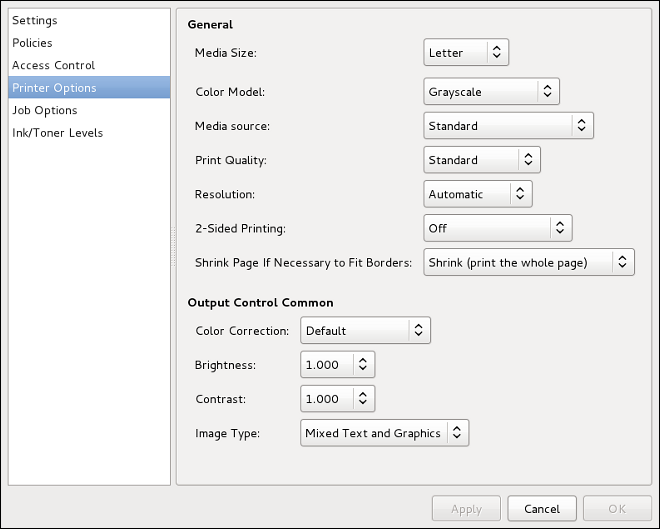
The Printer Options page contains various configuration options for the printer media and output, and its content may vary from printer to printer. It contains general printing, paper, quality, and printing size settings.
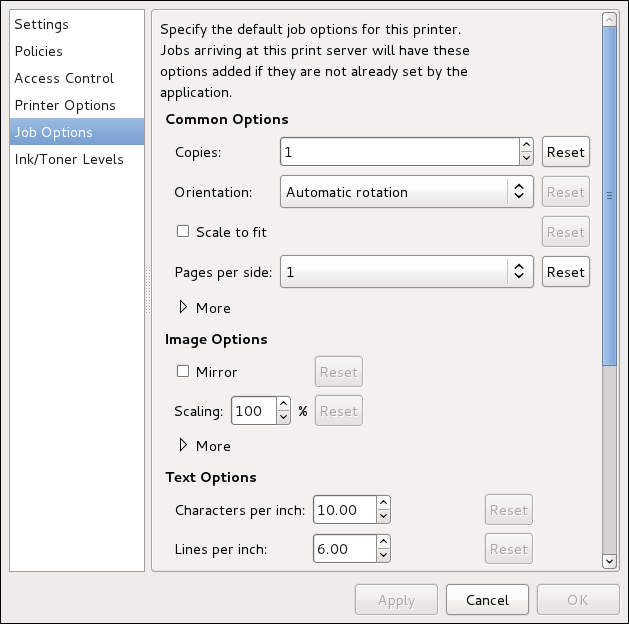
On the Job Options page, you can detail the printer job options. Click the Job Options label on the left to display the page. Edit the default settings to apply custom job options, such as number of copies, orientation, pages per side, scaling (increase or decrease the size of the printable area, which can be used to fit an oversize print area onto a smaller physical sheet of print medium), detailed text options, and custom job options.
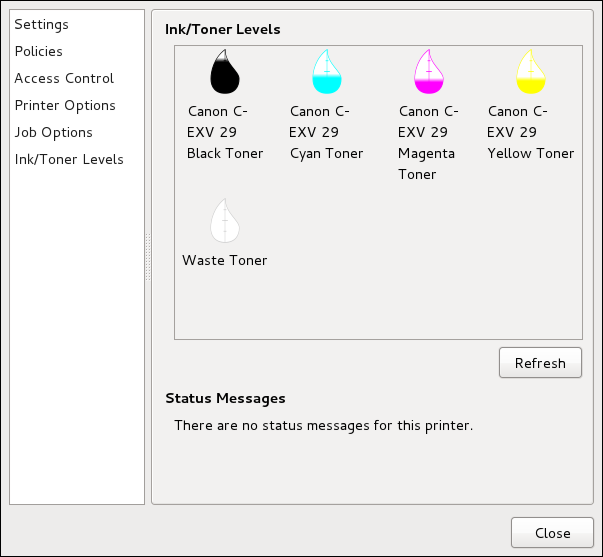
The Ink/Toner Levels page contains details on toner status if available and printer status messages. Click the Ink/Toner Levels label on the left to display the page.
Managing Print Jobs
When you send a print job to the printer daemon, such as printing a text file from Emacs or printing an image from GIMP, the print job is added to the print spool queue. The print spool queue is a list of print jobs that have been sent to the printer and information about each print request, such as the status of the request, the job number, and more.
During the printing process, messages informing about the process appear in the notification area.
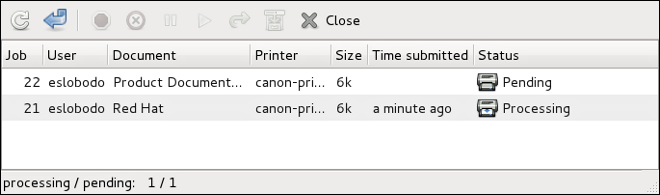
To cancel, hold, release, reprint or authenticate a print job, select the job in the GNOME Print Status and on the Job menu, click the respective command.
To view the list of print jobs in the print spool from a shell prompt, type the command lpstat -o. The last few lines look similar to the following:
$ lpstat -o
Charlie-60 twaugh 1024 Tue 08 Feb 2011 16:42:11 GMT
Aaron-61 twaugh 1024 Tue 08 Feb 2011 16:42:44 GMT
Ben-62 root 1024 Tue 08 Feb 2011 16:45:42 GMT
If you want to cancel a print job, find the job number of the request with the command lpstat -o and then use the command cancel job number. For example, cancel 60 would cancel the print job in Example of lpstat -o output. You cannot cancel print jobs that were started by other users with the cancel command. However, you can enforce deletion of such job by issuing the cancel -U root job_number command. To prevent such canceling, change the printer operation policy to Authenticated to force root authentication.
You can also print a file directly from a shell prompt. For example, the command lp sample.txt prints the text file sample.txt. The print filter determines what type of file it is and converts it into a format the printer can understand.
Recursos adicionais
To learn more about printing on Fedora, see the following resources.
Installed Documentation
- man lp
-
The manual page for the lpr command that allows you to print files from the command line.
- man cancel
-
The manual page for the command-line utility to remove print jobs from the print queue.
- man mpage
-
The manual page for the command-line utility to print multiple pages on one sheet of paper.
- man cupsd
-
The manual page for the CUPS printer daemon.
- man cupsd.conf
-
The manual page for the CUPS printer daemon configuration file.
- man classes.conf
-
The manual page for the class configuration file for CUPS.
- man lpstat
-
The manual page for the lpstat command, which displays status information about classes, jobs, and printers.
Useful Websites
- https://wiki.linuxfoundation.org/openprinting/start
-
Open Printing contains a large amount of information about printing in Linux.
- https://www.cups.org/
-
Documentation, FAQs, and newsgroups about CUPS.
Want to help? Learn how to contribute to Fedora Docs ›